Installing a BYOL Mist-managed Router in AWS
This guide describes the process for deploying a Mist-managed instance through AWS. When installed as an AWS image, SSR Version 6.x supports Mist-managed routers. The installation and deployment process consists of the following steps:
- Selecting the AMI.
- Deploying the Session Smart Router.
Proceed to the next section Selecting the AMI.
Selecting the AMI
Bring Your Own License (BYOL): This allows you to install your own licensed copy of the SSR software on an AWS VM. The device registration code is used to authenticate access to the Mist installation repositories. Refer to the Session Smart Networking Platform (BYOL) offering.
For the latest information about SSR BYOL offerings, please refer to the Cloud Images BYOL Release Notes.
Once you have selected the AMI that suits the needs of your deployment, proceed to the Session Smart Router Deployment to deploy a Session Smart Router.
Selecting the Instance Size
The following instance sizes are supported for virtual SSR in AWS. Choose the size that best meets your requirements. More information can be found in the AWS Documentation
| Recommended AWS VM Size | Max vNICs Supported | vCPU Cores | Memory |
|---|---|---|---|
| c5.xlarge | 4 | 4 | 8 |
| c5.2xlarge | 4 | 8 | 16 |
| c5.4xlarge | 8 | 16 | 32 |
| c5.9xlarge | 8 | 36 | 72 |
| c5n.xlarge | 4 | 4 | 10.5 |
| c5n.2xlarge | 4 | 8 | 21 |
| c5n.4xlarge | 8 | 16 | 42 |
| c5n.9xlarge | 8 | 36 | 96 |
Session Smart Router Deployment
Use the following steps to deploy a Mist-managed Session Smart Router in AWS.
Requirements
The following infrastructure must exist in your AWS account:
- A VPC where the Session Smart Router will be deployed.
- The existing VPC is segmented with the following subnets. The role of each subnet is described below.
- Public Subnet: This subnet must provide connectivity to enable communication with external/remote SSR peers as well as access to the Mist cloud infrastructure if no management subnet is provided.
- Private Subnet: This subnet must provide connectivity to internal workloads within the cloud.
- Management Subnet [Optional]: This subnet must provide connectivity to the Mist cloud and is reachable for SSH administration purposes.
- Enable enhanced network with ENA for maximum throughput performance. For SSR routers, execute the following command from your local computer
aws ec2 modify-instance-attribute --instance-id instance_id --ena-support
Please note that deploying Mist-managed Session Smart Routers is limited to deployments within the cloud. If you also require the deployment of an on-premises SSR, please contact your Juniper sales representative.
Deployment
A Session Smart Router can be deployed manually via the AWS Console or using AWS CLI commands. This section describes both methods. Choose the method that better suits your needs.
When deploying the Session Smart Router using the templates referenced in this section, the following infrastructure elements are created automatically to assist with the deployment process:
- EC2 instance using a Session Smart image available in the marketplace. When selecting a platform for deployment, Juniper recommends the use of an AWS EC2 instance size c5.xlarge, or larger.
- The router is deployed with appropriate network interfaces.
- Each network interface has a network security group associated. The network security groups are configured in accordance with the requirements to deploy a fabric with Session Smart Networking software.
- The public and management interfaces have a unique and static public IP address associated.
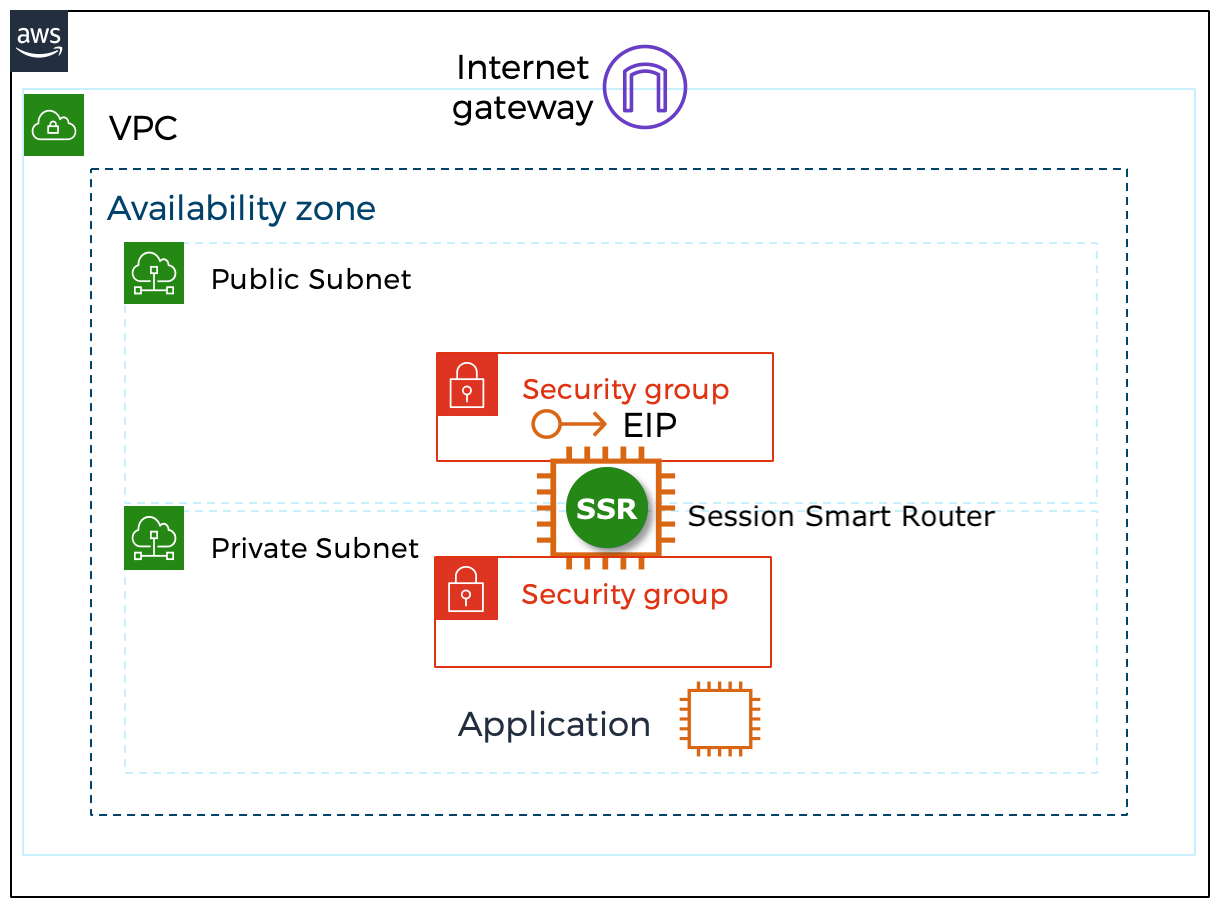
The following image shows the infrastructure elements deployed:
Using the AWS Console
To deploy the Session Smart Networking software via the AWS Console:
- Click on the Session Smart Networking Platform BYOL offering.
- Click on the Continue to Subscribe button and accept the terms and conditions.
- Click on the Continue to Configuration button.
- In the Fulfillment Option drop down box select CloudFormation Template, select the template Juniper Session Smart Mist Managed Router and select the desired region.
- Click on the Continue to Launch button.
- In the Choose Action box, select Launch CloudFormation and click on the button Launch.
- Answer the following questions to launch the deployment of an SSR. For a description of the parameters of the template, please refer to Launch the Template.
- What name do you want to give the instance?
- Provide it in the Router Name field (for example: SSR_1_Router).
- Which Mist organization is going to manage it? Provide the registration code for the Mist organization.
- What version of SSR software do you want to install?
- Who is going to be the administrator?
- Select the IAM user key.
- Where do you want to deploy it?
- Select the VPC in the region.
- Select the public, private, and optional management subnets within the VPC.
- Click the Next button.
- Click on the Create stack button to launch the deployment.
Once the deployment completes, information is provided in the Outputs tab, and the Zero Touch Provisioning (ZTP) installation process begins. After the VM is deployed, an additional 2-3 minutes are required before the ZTP process initializes. When the ZTP process is ready, there will be an asset in the Mist inventory to be associated with the router configuration. It will then take an additional 5-10 minutes for the desired SSR version to be installed.
Using the AWS CLI
To deploy the Session Smart Networking software via the AWS CLI:
- Click on the Session Smart Networking Platform BYOL offering.
- Click on the Continue to Subscribe button and accept the terms and conditions.
- Click on the Continue to Configuration button.
- In the Fulfillment Option drop down box select CloudFormation Template, select the template Juniper Session Smart Mist Managed Router and select the desired region.
- Click on the Continue to Launch button.
- In the Choose Action box, select Launch CloudFormation and click on the button Launch.
- Copy to the clipboard the URL of the template located in the field Amazon S3 URL.
Launch the deployment with the corresponding AWS CLI commands making use of the S3 URL of the template identified previously. For a description of the parameters of the template, please refer to Launch the Template.
Cloud-init Onboarding
When launching an AWS EC2 instance using automation the following user-data section can be leveraged to setup the onboarding data for the instance.
#cloud-config
write_files:
- path: /etc/128T-hardware-bootstrapper/onboarding-config.json
content: |
{ "name": "<router-name>", "ssr-version": "<version>", "registration-code": "<regcode>", "mode": "mist-managed", "cloud-provider": "aws"}
| Option | Meaning |
|---|---|
| name | The name of the router to use for Mist onboarding. By default, the instance name will be used. |
| registration-code | The Mist registration used for adoption of the EC2 instance to a Mist organization. |
| ssr-version | The SSR software version to be installed on the instance. (BYOL only) |
Manual Onboarding
If a user does not supply the onboarding configuration before launching the instance, the onboarding steps can be manually executed.
- Log into the instance using the default SSR username
t128and the key pair provided when launching. - Run
/usr/libexec/hardwareBootstrapper128t config-generator - Follow the prompts to generate and apply the onboarding configuration.
Mist-Managed Setup
Once the EC2 instance is launched with the correct registration-code, the device will self-onboard to the appropriate Mist organization. The device is visible as Unassigned in the Mist organization once onboarding is complete. At this point, the SSR install process will begin. This process can take up to 15 minutes to complete. Once complete the Version will be populated in the Mist inventory.
If the device does not show up in the Mist organization or the desired SSR version was not installed after 15 minutes, SSH into the instance. If the instance was created using the BYOL template, the default username will be t128. If not, the username will be ec2-user.
-
Try to log into the pcli, run
su adminand thenshow mist. -
If the pcli is not accessible or the status and necessary action is not obvious, unzip the Hardware Bootstrapper tech support (
/var/log/128T-hardware-bootstrapper/hardware-bootstrapper-tech-support.zip) and examine the journal for128T-hardware-bootstrapper,ember, and128T-mist-agent.
Network Interfaces Layout
The Session Smart Router Template deploys an EC2 instance for the SSR with two network interfaces and an optional third management interface. The template attaches the network interfaces to the EC2 instance in the following order: Management (Optional), Public, Private.
If a management network interface is provided, the names to be used in the Mist configuration are as follows:
| Network Interface Name | Subnet | Mist Config Name |
|---|---|---|
| ge-0-0 | Management | Out Of Band Management |
| ge-0-1 | Public | ge-0/0/1 |
| ge-0-2 | Private | ge-0/0/2 |
If no management network interface is provided, the names to be used in the Mist configuration are as follows:
| Network Interface Name | Subnet | Mist Config Name |
|---|---|---|
| ge-0-0 | Public | ge-0/0/0 |
| ge-0-1 | Private | ge-0/0/1 |
| ge-0-2 (If Applicable) | HASync | ge-0/0/2 |
| ge-0-3 (If Applicable) | HAFabric | ge-0/0/3 |
Interface Tagging
In addition to using the cloud formation template, the admin can tag the interface with the key SSR-ROLE. The possible values are as follows:
| Tag Value | Meaning |
|---|---|
| WAN | Interface is marked as WAN for onboarding purposes. Without a MGMT interface, it is assumed to have connectivity to Mist cloud infrastructure. |
| LAN | Interface is marked as LAN and is assumed to be used as a private network for internal workflows. |
| MGMT | Interface is marked as MGMT and is assumed to have connectivity to Mist cloud infrastructure and SSH access prior to site assignment. |
| HAFabric | Interface is marked as HAFabric and is used as the fabric link in an HA deployment. |
| HASync | Interface is marked as HASync and is used as the redundancy link in an HA deployment. |
The EC2 instance must be assigned the IAM role containing the ec2_describeNetwork permission to leverage the interface tagging. This is automatically done when using the provided templates.
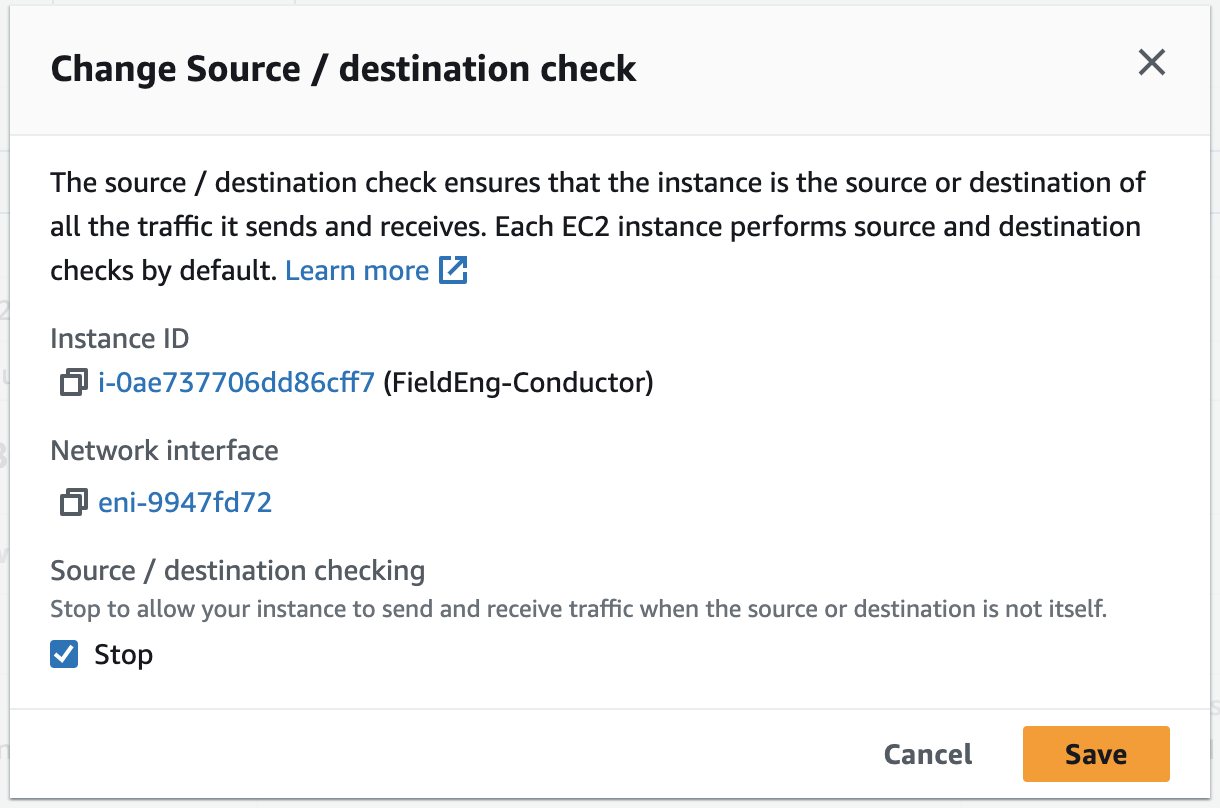
Source / Destination Check
Disabling Source / Destination checking allows the SSR AWS instance to send and receive traffic when it is not the source or destination. This feature is enabled by default. Perform the following steps to disable Source / Destination checking.
- On the Instances page, select the Launch Instances dropdown.
- Select Networking.
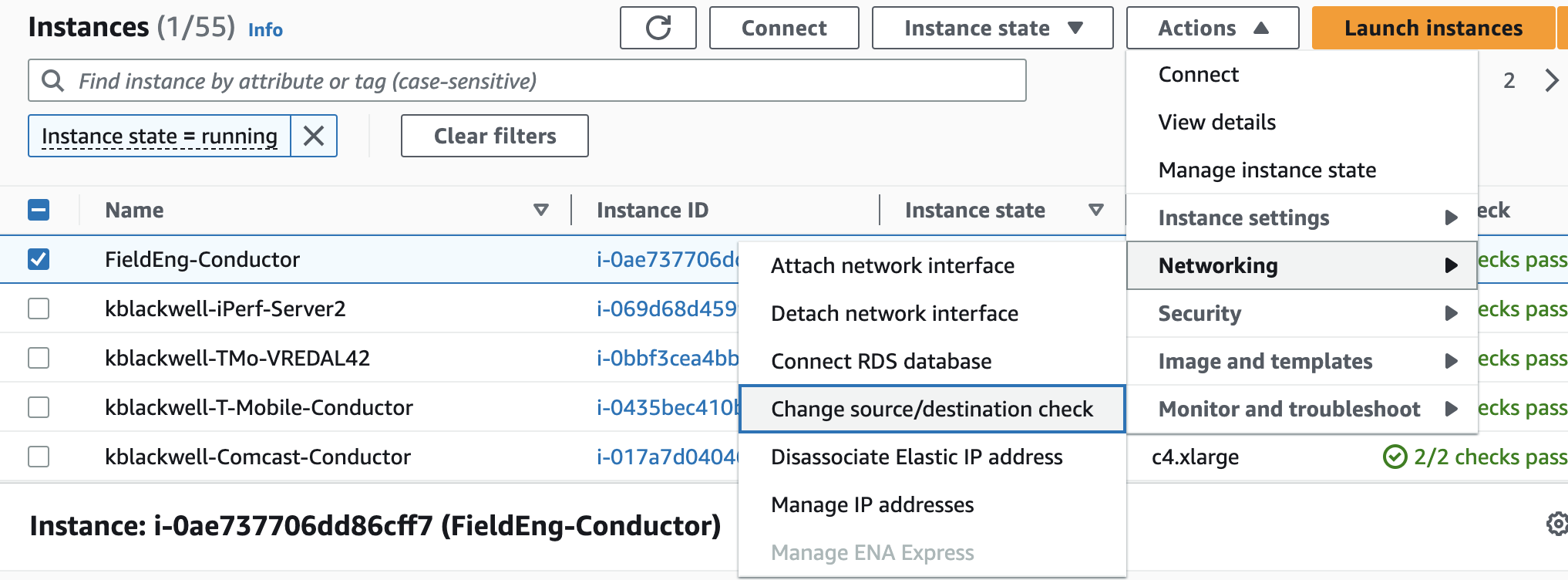
- From the pull out menu, select Change source/destination check.
- In the Change Source / Destination Check window, select Stop, and Save.
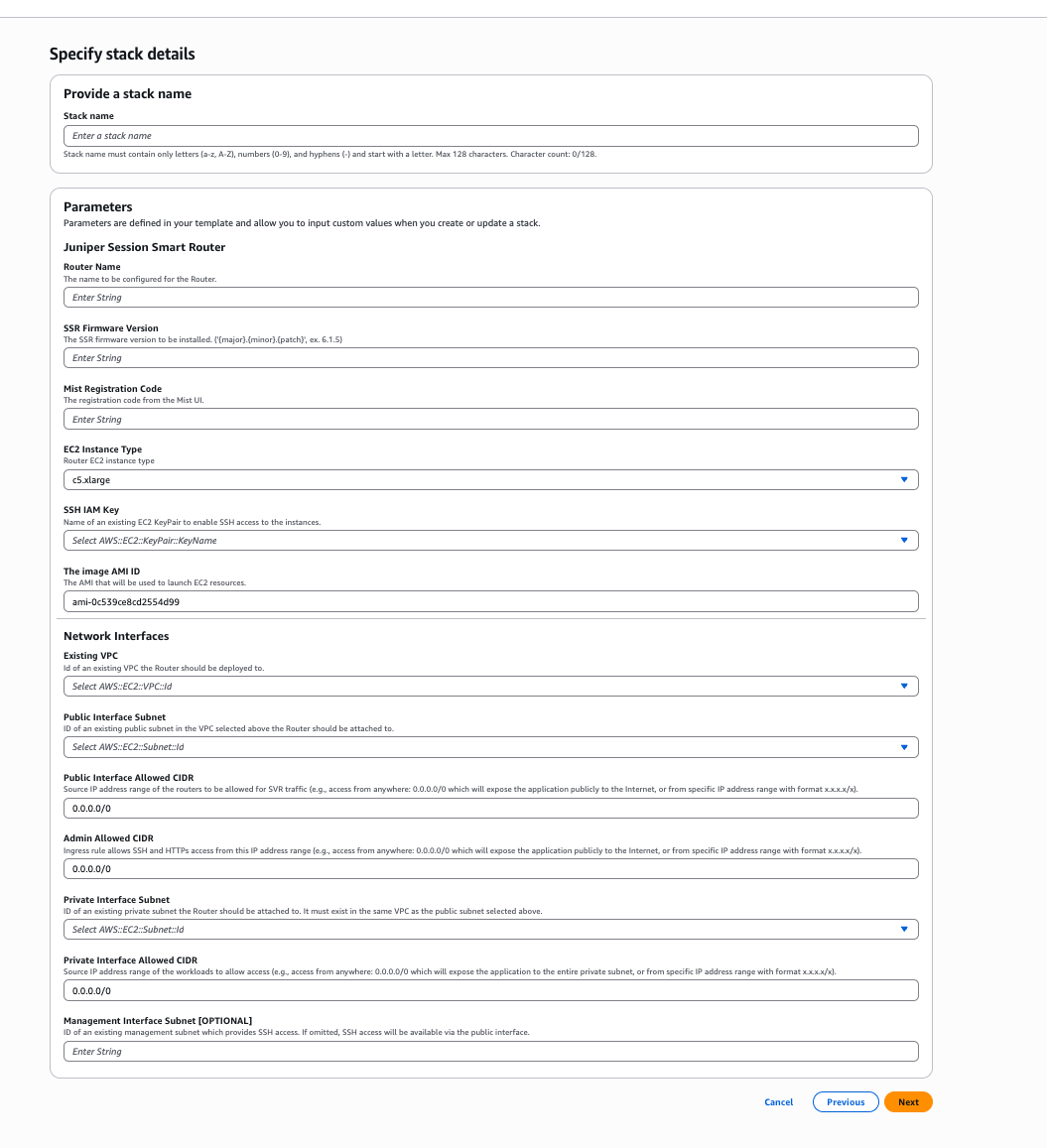
Launch the Template
This section describes the parameters to complete the template to deploy a Mist-managed SSR, as well as how to launch it using the portal or programmatically.
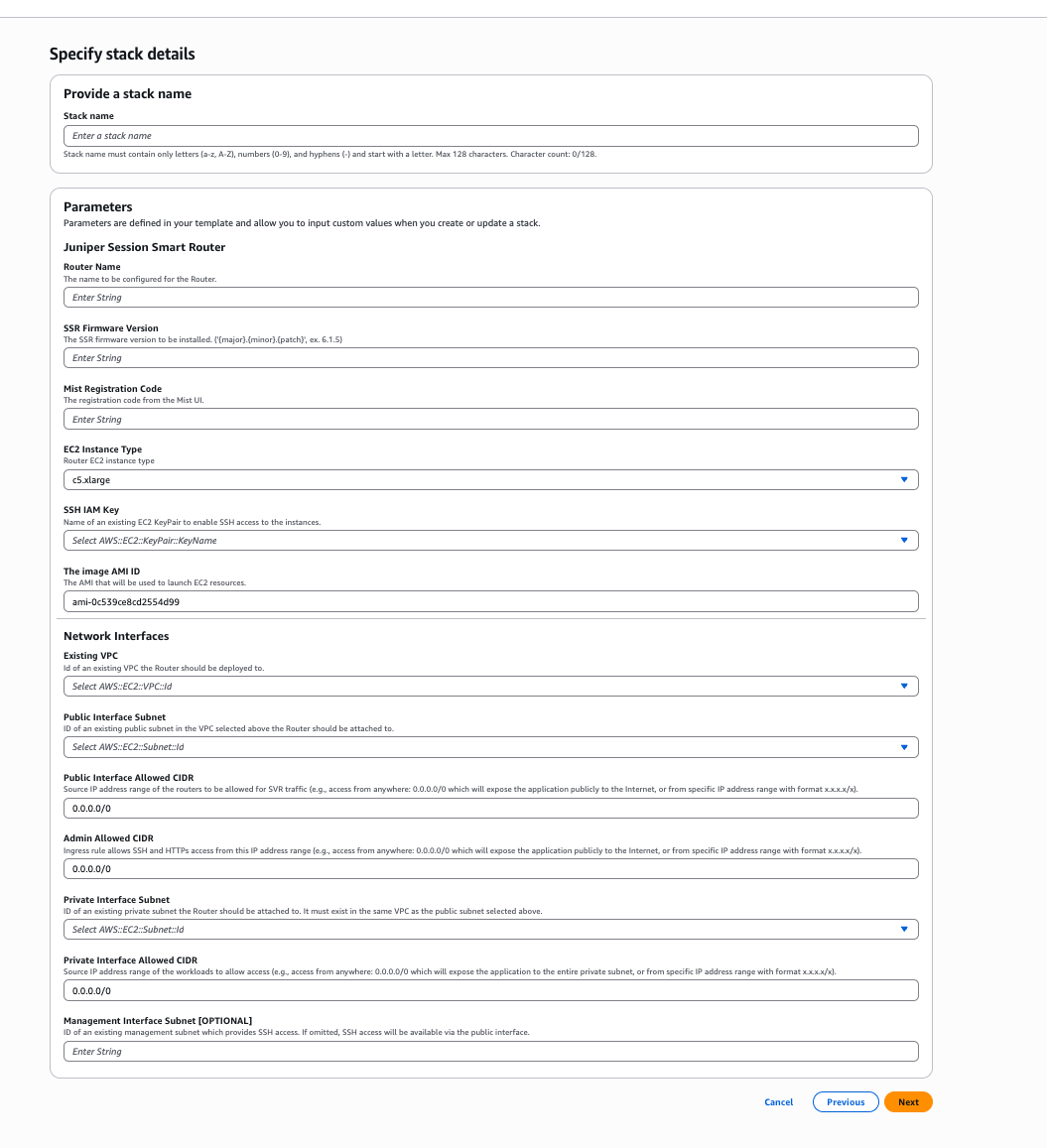
A description of the parameters of the template are listed in the following table:
| Parameter | Description |
|---|---|
| Router Name | Name of the VM for the Mist-managed router. |
| Version | SSR software version installed on the instance. |
| Registration Code | The Mist registration used for adoption of the EC2 instance to a Mist organization. |
| Instance size | Size of the EC2 instance. |
| SSH IAM Key | IAM user key (SSH public key) to login to the EC2 instance (Linux) via SSH. |
| VPC ID | ID of the existing VPC where the Mist-managed router is going to be deployed. |
| Public Interface Subnet | ID of the public subnet within the VPC. |
| Public Interface Allowed CIDR | The IP CIDR range of the endpoints allowed to originate traffic to the Router's public interface in the public subnet. |
| Admin Allowed CIDR | The IP CIDR range of the endpoints allowed to SSH to the EC2 instance as well as login to the Router's GUI. |
| Private Interface Subnet | ID of the private subnet within the VPC. |
| Private Subnet Allowed CIDR | The IP CIDR range of the endpoints allowed to originate traffic to the Router's private interface in the private subnet. |
| Management Interface Subnet [OPTIONAL] | Optional ID of the management subnet within the VPC. |
AWS Console
- Go to the Session Smart Networking Platform BYOL offering following the steps described in the section Selecting the AMI.
- Click on the Continue to Subscribe button and accept the terms and conditions.
- Click on the Continue to Configuration button.
- In the Fulfillment Option drop down box select CloudFormation Template, select the template Juniper Session Smart Mist Managed Router and select the desired region.
- Click on the Continue to Launch button.
- In the Choose Action box, select Launch CloudFormation and click on the button Launch.
- Click the Next button.
- Fill out the template. Review the section above to understand the parameters of the template.
- Continue clicking the Next button.
- Click Create Stack to start the deployment.
Once the deployment of the template is complete, information about the new router deployment is provided in the Output tab.
The information listed in the Outputs tab is the following:
- Instance ID of the Router EC2 instance.
- Public IP address of the public interface for administration purposes.
- SSH command to login to the Linux VM.
AWS CLI
Alternatively, it is possible to launch the template programmatically. Please adjust the content of the JSON file below to match the input of each template.
Create the parameters file router.parameters.json with the following command:
vi router.parameters.json
Paste the following JSON content. Please adjust the values to your specific environment:
{
"Name": "<instance name>",
"Version": "<ssr-version>",
"RegistrationCode": "<Registration-code>",
"InstanceType": "c5n.xlarge",
"KeyName": "<ssh-key-name>"
"VpcId": "<ID of the VPC>",
"PublicSubnet": "<ID of the public subnet within the VPC>",
"PublicSubnetAllowedCidr": "0.0.0.0/0",
"AdminAllowedCidr": "0.0.0.0/0",
"PrivateSubnet": "<ID of the private subnet within the VPC>",
"PrivateSubnetAllowedCidr": "0.0.0.0/0",
"ManagementSubnet": "<Optional ID of the management subnet within the VPC>"
}
- Go to the Session Smart Networking Platform BYOL offering following the steps described in the section Selecting the AMI.
- Click on the Continue to Subscribe button and accept the terms and conditions.
- Click on the Continue to Configuration button.
- In the Fulfillment Option drop down box select CloudFormation Template, select the template Juniper Session Smart Router and select the desired region.
- Click on the Continue to Launch button.
- In the Choose Action box, select Launch CloudFormation and click on the button Launch.
- Copy to the clipboard the URL of the template located in the field Amazon S3 URL.
Launch the template running the following command:
aws ec2 create-launch-template \
--launch-template-name <template-file> \
--launch-template-data file://router.parameters.json
Deploying a Router without Templates
- Launch a web browser and navigate to https://aws.amazon.com/
- Login to AWS with your account.
note
If you do not have an account, click Create an AWS Account to register.
- Click EC2 Dashboard and select your deployment region from the drop down list.
- Click Launch Instance.
- On the Step 1: Choose an Amazon Machine Image (AMI) page, select the Amazon Marketplace tab and enter Session Smart Networking in the search bar.
- Locate the SSR image and click Select.
- On the Step 2: Choose and Instance Type page, choose an instance type.
- On the Step 3: Configure Instance Details page, click Subnet and select the desired subnet and retain the default values for the other fields.
note
If the desired subnet is not listed, click Create New Subnet to create one.
- Click Next: Add Storage.
Select Yes, I want to continue with this change and click Next.note
The You have changed your network setting window may appear.
- On the Step 4: Add Storage page, ensure the size is 128 GB (default value).
- Click Next: Add Tags. See Interface Tagging for additional tag configuration information.
- On the the Step 5: Add Tags page, click Add Tags.
- Click inside the Key column and select Name. Under the Value column enter the name for your instance.
- Click Next: Configure Security Group.
- On the Step 6: Configure Security Group page, click select an existing security group and choose one from the list.
note
If the desired security group is not listed you can create your own by selecting Create a new security group and following the prompts.
- Expand the Advanced Details and scroll down to the User data section. To onboard the router to the desired Mist organization, you can add cloud-init user-data using the steps in the Cloud-init Onboarding section.
- Select Review and Launch.
- In the Boot from General Purpose window, select Continue and then click Next.
- On the Step 7: Review Instance Launch page, click Launch to finalize the instance.
- In the Select an existing key pair or create a new key pair dialog box, select Choose an existing key pair and select the desired key pair from the list.
note
If the desired key pair is not listed click Create a new key pair, enter a name in the Key pair name field and click Download Key Pair.
- Check the acknowledgment check box and then click Launch Instances.
- If an onboarding configuration was not provided in step 16, follow the steps in the Manual Onboarding section.
Configuring a Default Route to an Internet Gateway
If the EC2 instance deployed for the Session Smart software does not have access to the Internet, verify a default route to an Internet Gateway exists:
- From the main toolbar, click Services to expand the Services list and select VPC.
- From the VPC Dashboard pane, click Your VPCs.
- From the VPC Dashboard pane, click Route Tables and then Create Route Table.
- In the Create Route Table dialog box, enter the following information and click Yes, Create.
- Name Tag: Enter a name for your route table
- VPC: Using the dropdown list, select the VPC to associate with the route table
- From the VPC Dashboard pane, select Internet Gateways and click Create Internet Gateway.
- In the Create Internet Gateway dialog box, enter an Internet Gateway name in the Name Tag field and click Yes, Create.
- On the Internet Gateways page, click Attach to VPC and assign the Internet Gateway to your VPC.
- From the VPC Dashboard pane, select Route Tables and click Edit.
- Click Add Another Route.
- In the 0.0.0.0/0 row, click the empty cell under the Target column and the local name automatically appears as a selectable option.
- Select it and click Save.
Deploying an HA Mist Managed Session Smart Router
To deploy an HA Mist Managed Router, you must deploy the CloudFormation template directly.
- Launch a web browser and navigate to https://console.aws.amazon.com/cloudformation.
- Click Create stack and With new resources (standard).
- Paste the following S3 URL into the Amazon S3 URL dialog.
https://ssr-templates.s3.us-east-1.amazonaws.com/aws-byol-ha-mist-managed-router-template-ssr-byol-4.0-20251211-1429-2.json
- Click next and complete the form.
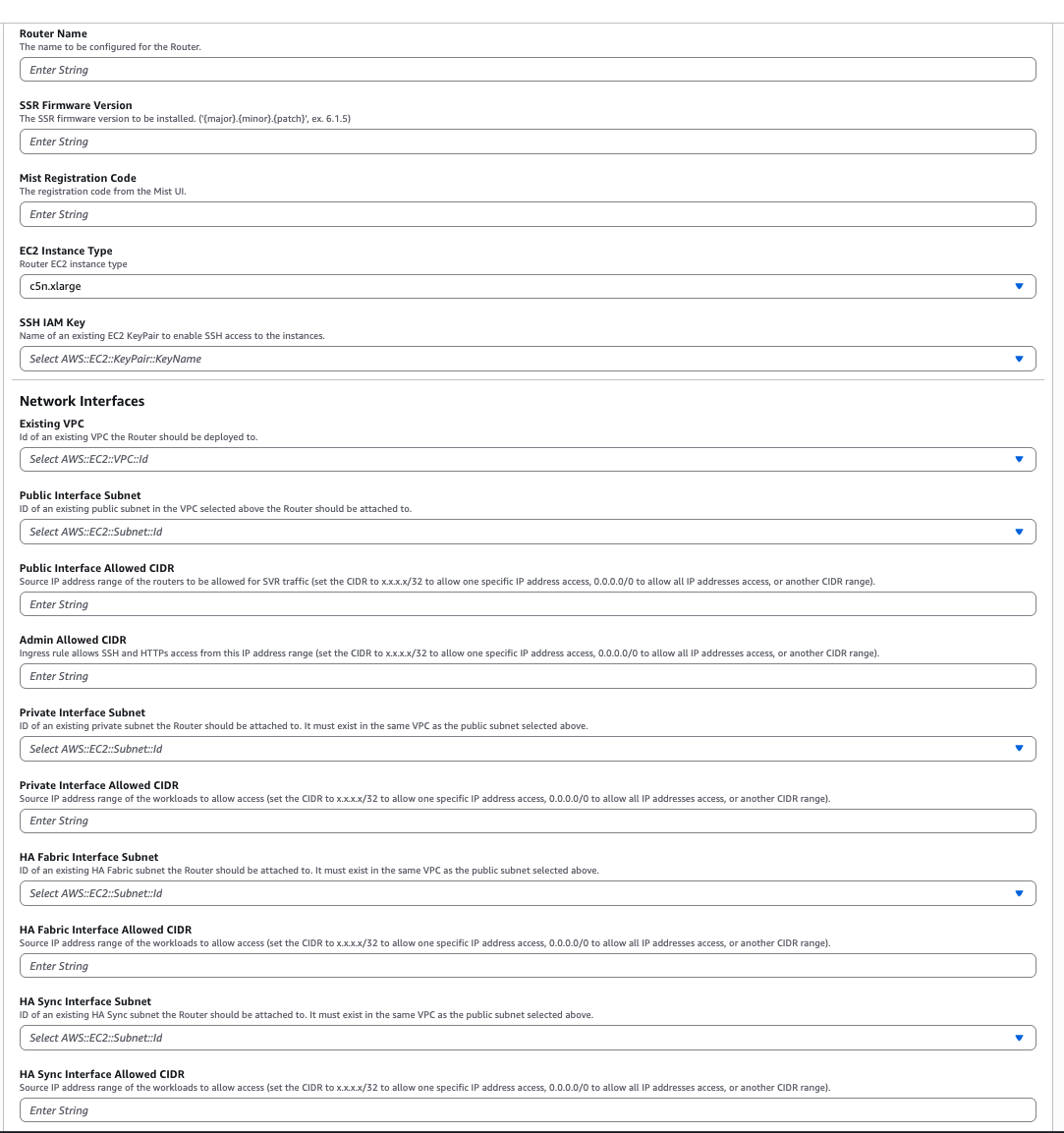
A description of the parameters of the template are listed in the following table:
| Parameter | Description |
|---|---|
| Router Name | Name of the VM for the Mist-managed router. |
| Version | SSR software version installed on the instance. |
| Registration Code | The Mist registration used for adoption of the EC2 instance to a Mist organization. |
| Instance size | Size of the EC2 instance. |
| SSH IAM Key | IAM user key (SSH public key) to login to the EC2 instance (Linux) via SSH. |
| VPC ID | ID of the existing VPC where the Mist-managed router is going to be deployed. |
| Public Interface Subnet | ID of the public subnet within the VPC. |
| Public Interface Allowed CIDR | The IP CIDR range of the endpoints allowed to originate traffic to the Router's public interface in the public subnet. |
| Admin Allowed CIDR | The IP CIDR range of the endpoints allowed to SSH to the EC2 instance as well as login to the Router's GUI. |
| Private Interface Subnet | ID of the private subnet within the VPC. |
| Private Subnet Allowed CIDR | The IP CIDR range of the endpoints allowed to originate traffic to the Router's private interface in the private subnet. |
| HA Fabric Interface Subnet | Optional ID of the management subnet within the VPC. |
| HA Fabric Interface Allowed CIDR | The IP CIDR range of the endpoints allowed to originate traffic to the Router's HA Fabric interface. |
| HA Sync Interface Subnet | Optional ID of the management subnet within the VPC. |
| HA Sync Interface Allowed CIDR | The IP CIDR range of the endpoints allowed to originate traffic to the Router's HA Sync interface. |
- An HA Mist Managed router will be deployed with network interfaces according to Network Interfaces Layout.